
EX Series
Bandwidth and Links Management with Identity

Click here to jump to more pricing!
Overview:
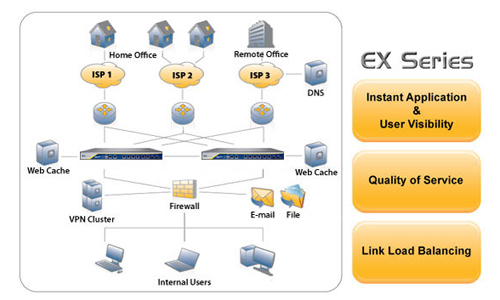
The EX Series is the industry's only appliance combining bandwidth management, link management, and network monitoring with application and user visibility. This helps organizations optimize and secure their networks by understanding their current network demands at the application and user level, applying traffic policies to enforce network utilization, and increasing reliability of traffic through the use of application prioritization and multiple links. The EX series is built on a high performance and secure platform for an unmatched solution to optimize the network edge.

Bandwidth Management
Comprehensive Protocol Support: Maximize bandwidth with support for over 100 applications to ensure the most critical network traffi c receives the highest priority across WAN links. The EX provides automatic application protocol classifi cation, comprehensive policies and traffi c controls such as rate shaping, rate limiting, selective dropping, priority marking and automatic load aware shaping.
Application Protocol Identification: Application protocol classifi cation techniques extend above simple Layer 3 and 4 (IP and port) combinations. Deep packet inspection techniques enable the EX to identify application protocols for positive application identifi cation. These techniques enable the EX to identify application protocols that use port hopping, port tunneling, and encryption.
Innovative User Based QoS Policies: Allocate bandwidth and network application access transparently to a user based solely on their company assigned user ID. Practically any corporate data store such as Active Directory, SQL database and LDAP is available when connecting to an A10 ID Series appliance. Traditional QoS policies based on Layer 3-7 traffi c classifi cation and heurstics can also be used to control bandwidth consumption.
Application & User Visibility
Bandwidth Utilization Reports: Bandwidth utilization reports quickly identify top applications, and users consuming the most bandwidth. Graphical real-time and historical reports with drill down capabilities are available from the web user interface. PDF, HTML or XML formatted reports may be exported manually or emailed periodically on a confi gurable schedule.
Identity-Based Application Visibility: Know who is doing "what" and "when" by monitoring application activity and application user identities for a variety of Instant Messaging (IM), fi le transfer, and email applications. Combine with A10's ID Series appliance to enhance all reports and policies with a company assigned identity, machine host name, and MAC address for unprecedented visibility and control.
Application Logging: Log discrete application actions with user name, such as writing a fi le, sending an email or posting data to a web site, and archive them periodically for compliance or post event investigations. Use a free form text search engine to pinpoint events of interest.
Link Management
Link Load Balancing: Support multi-homed networks with fi negrained load balancing across two or more WAN links to help increase WAN capacity, ensure link level redundancy and optimize network traffi c over the WAN. The EX allows mission critical applications to use highly available dedicated links and noncritical applications such as web browsing or multimedia to use links with lower service level agreements.
Performance, Security & Flexibility
High Performance: 1 Gbps to 4 Gbps throughput allows the network capacity room to grow and scale with increasing needs.
Network IPS: Identify network anomalies before they impact your internal machines. Provide real time protection against attacks such as Distributed Denial of Service (DDoS), port scans, address sweeps, protocol misuse and malformed packets.
Flexible Deployment Options: Integrate into existing network infrastructures with support for both transparent and gateway modes, allowing fail open or closed confi gurations. Transparent mode also means no network confi guration is changed for seamless deployment.
With the EX Series' advanced feature-chaining capabilities, customers can mix and match EX Series features to customize WAN management solutions to fit their network requirements without sacrificing performance or adding unnecessary latency–unlike implementing point play products from multiple vendors.
Features:
Application Bandwidth Management
- QoS policy actions
- Automatic load aware shaping
- Rate shape, limit, drop
- Connection limit
- Priority marking
- Apply sub-policy
- QoS policy rules
- 100+ predefined application classes
- Custom classes based on L2-L7 attributes
- Custom classes based on Identity
- aFleX powered custom classification engine
- Heuristics based classification
- Predefined application class categories
- Peer-to-Peer (Ares, BitTorrent, Cspace, Dijjer, DirectConnect, eDonkey-eMule, FreeCast, Gnutella, Limewire, KaZaA, Krawler, PPLive, PPStream, Share, SoulSeek, TVAnts, WinMX, Xunlei)
- Multimedia (Abacast, Flash Video, iTunes, Motion, Quicktime, RTP, RTSP, Shoutcast, Windows Media)
- Voice-over-IP (H323, Skype, Skinny)
- Instant Messaging (AOL, Yahoo, MSN, Gtalk, IRC, QQ)
- Access (SSH, rlogin, telnet, Remote Desktop, VNC) File Transfer (FTP, RCP, NFS, CIFS, SMB, NetBIOS, Netware)
- Email (MS Exchange, POP3, IMAP, SMTP, BIFF)
- Database (mySQL, Oracle)
- Directory (LDAP, ident)
- Web (HTTP, HTTPS)
- Miscellaneous (AURP, Ariel, BGP, Day Time, DHCP, DNS, Echo, Gopher, Kerberos, Lotus, IPP, NNTP, NTP, Printer, RPC, RPC2Portmap, Router, Shell, SNMP, Sun RPC, Syslog, Time, UUCP )
Link Management
- Inbound and outbound WAN link balance
- Link preference by QoS class
- Bind different classes to different link sets
- Expose internal services using Destination Network Address Translation (DNAT) or server load balancing (SLB)
- Use built in DNS or 3rd party DNS
- Packet steering or link load balance by domain name or identity
- Link load balancing algorithms
- Round Robin
- Weighted Round Robin
- Least Connection
- Weighted Least Connection
- Bandwidth Usage
- Round Trip Time
- Bandwidth Price
Application and Identity Visibility
- Granular reporting
- Top N internal talkers
- Top N external talkers
- Top N applications
- Top N URLs
- Packet size distribution
- Interactive drill down
- Periodic graphical reports
- Threshold alerts
- Enhanced with Identity, Client Host Name, and Client Host MAC address
- PDF, HTML or XML format
- By application, subnet, VLAN or interface
- Application logging
- File Transfer – FTP, NFS, CIFS
- Mail - SMTP, POP3
- Instant Messaging – Yahoo, AOL, MSN, QQ
- Web – HTTP Post
- Map application ID to company assigned ID
- Augmented with ID, host name, and MAC
IPS Anomaly Protection
- 28 network anomaly types
- DDoS Attacks
- ICMP Based Attacks
- IP Based Attacks
- TCP/UDP Based Attacks
Layer 2 and Layer 3 Support
- L3 routing protocols
- RIP2
- OSPF
- Static Route
- L2 transparent mode
- Tagged and untagged Vlans
Management
- Industry standard Command Line Interface (CLI)
- Intuitive Graphical User Interface (GUI)
- Localized for Chinese, Japanese and Korean
- SSH, Telnet, RS-232 Serial Console
High Availability
- Active/Standby
Specifications:
| Ex Series Models | ||
|---|---|---|
| EX 1100 | EX 2110 | |
| Model Option Code | Single Quad Core | Single Quad Core |
| Ethernet Interface Gigabit Copper Gigabit Fiber – SFP Mini GBIC |
4 0 |
6 2 |
| Management Interface | Yes (separate port) | Yes (separate port) |
| Console Port | Yes | Yes |
| Hard Disks | Single | Single |
| Cooling Fan | Single, Fixed | Single, Fixed |
| Maximum Power Consumption | 131 W | 158 W |
| Power Supply | 250 W | Dual 600 W RPS |
| 100 to 240 VAC, Frequency 50 – 60 Hz | ||
| Power Off Bypass | Yes | Yes |
| Dimensions | 1.75 in (H) x 17.3 in (W) x 16.7 in (D) | 1.75 in (H) x 17.3 in (W) x 16.7 in (D) |
| Rack Units (Mountable) | 1 U | 1 U |
| Unit Weight | 16 lb | 16 lb |
| Operating Ranges | Temperature and Humidity 0° - 40° C 5% - 95% | |
| Regulatory Certification | FCC Class A, UL, CE, TUV, CB, VCCI | |
| Standard Warranty | 90-day Hardware & Software | |
Videos:
Documentation:
Download the EX Series Datasheet (PDF).
- Pricing and product availability subject to change without notice.

